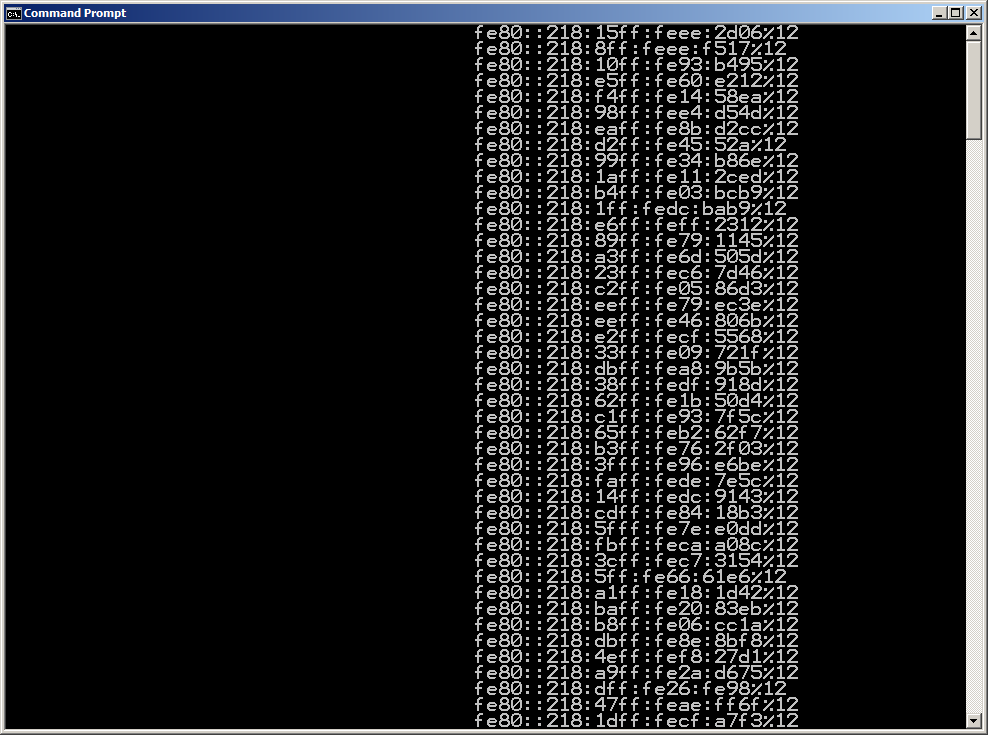
A couple of hours ago Christopher (Werny) and I gave this presentation at the Heise IPv6-Kongress, which overall was a quite interesting and well-organized event bringing together a number of practitioners from the field. While yesterday’s talks were dominated by a certain euphoria and optimistic pioneer spirit, the second day featured some security talks which induced slight shadows to the brave new world of IPv6 ;-). I particularly enjoyed meeting Eric Vyncke from Cisco (one of the two authors of this great book) and Marc “van Hauser” Heuse who released a new version of the THC-IPV6 tool set today. We had some fruitful discussions and we took the opportunity to test some of his newly implemented attacks against “RA Guard” running on a 4948E Chris and I had brought for a demo within our talk. Unfortunately – or fortunately in terms of a “from theory to reality” approach – I have to say that Marc found a quite clever way to circumvent RA Guard by putting the actual “RA payload” into a second frame following a first one mostly containing a “long & empty” destination option (after a fragmentation header pointing to the mentioned second one). To get an idea pls see these screenshots from Wireshark. 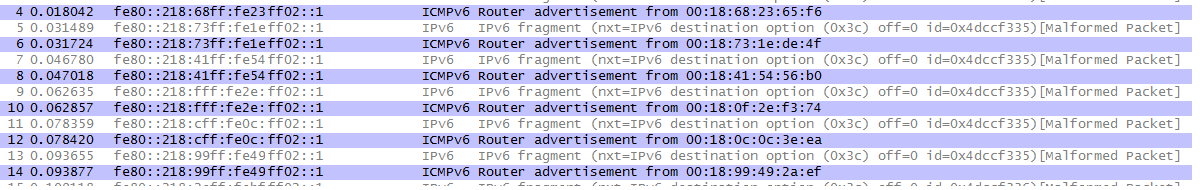
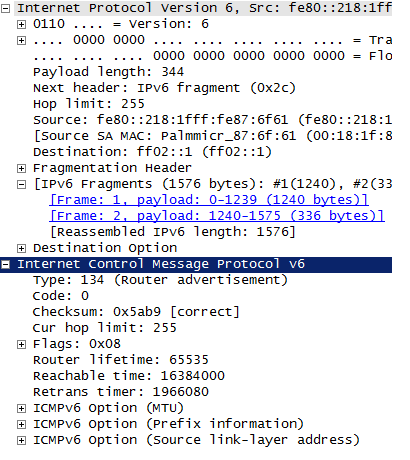
This actually completely defeats (the current implementation of) RA Guard which means that the victim machine received a whole lot of router advertisments…
Eric who gave an excellent talk on his own (mostly covering defense techniques but, amongst others, describing some interesting attacks against tunnel technologies, which btw reminds me I still owe you a blogpost on those… trust me: it’s not forgotten ;-)) stated that this specific type of attack could be mitigated by using an ACL containing sth along the lines of
deny ip any any undetermined-transport
[which is supposed to match any IPv6 packet where the upper-layer protocol cannot be determined].
We (Christopher and I) weren’t even aware of that keyword and we did not yet have an opportunity to test its effectiveness. Still there’s some immediate lessons to be learned from those hours in Frankfurt:
a) in the field of IPv6 security one can learn something new every day 😉
b) there’s still so much “uncovered space” in the IPv6 (security) world that we’ll certainly see yet-unknown types of attacks in the next years.
c) Marc is a really smart guy (which prompted me inviting him to speak at next year’s Troopers ;-))
d) Going with ACLs on “access layer”/customer/subscriber facing ports might be the better approach than just using RA Guard. (on a related note: some Cisco guy I talked to was very sceptical that RA Guard will ever be available on 2900 or 3500 series switches).
Most probably this ([1], [2], [3]) little sequence of IPv6 related posts will be continued soon (but not before we’ve finished the update of the “Attacking 3G and 4G networks” talk to be given at HITB Amsterdam next Friday ;-)).
Have a great weekend everybody
Enno
It says malformed packet on frames 5,7,9…
I tried some different attacks with the same approach (fragmentation and large destination options) but I wasn’t able to generate a packet that Wireshark will not mark malformed. Do you have any idea what Wiresharks complains about?
Btw, I was at that conference too, are your screenshots from Marcs live demonstration or have you been reproducing the setup?
Thanks!
Hi,
sorry for the late reply, life kept me (too) busy. As for your questions:
a) I think Wireshark complains as it does not expect to see an IPv6 packet without an actual upper layer payload. As, obviously, the RA guard implementation on the Cisco device in question (a 4948-E) doesn’t either (expect this). Still the packets are not malformed, it’s just Wireshark not fully understanding them.
b) the screenshots are from a litte session in the break right before Marc’s talk. We (he & us) gathered and did some testing with his tool and our device. Did he give a live demo of this one? I’d expect this not to have happened (lacking a RA guard capable device) but I changed rooms at noon to follow Eric’s talk so couldn’t see Marc’s talk in full.
Feel free to contact us directly (erey@ernw.de, cwerny@ernw.de) to discuss this further.
thanks
Enno